This article will cover setting passwords on a router / Switch at a CCNA level. TACACS and RADIUS will be covered in a future article.
The Enable password:
the Enable password protects privileged mode of the Router / Switch. This is where configuration changes can be made. This password can be cnfigured as an encrypted password or as plain text.
To configure in plain text use:
enable password
To configure in encrypted mode use:
enable secret
The Enable Password is un-encrypted and can be seen in the running config in plain text as shown.
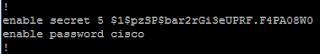
The Enable Secret looks like this in the running Config:
The enable secret password is encrypted with an MD5 hash and is very secure. In production, this is the password to use. There is no reason to have a plain text enable password in your config, as this will be over ruled by any enable secret that is in place. In a running config it looks like this:
You can encrypt plain text passwords with the service password-encryption command, however this is not as secure as the Enable Secret. The Service password-encryption command is a simple Vigenere cipher and is intended for line of sight protection. several websites are available that will break one of these passwords with no effort at all.

Console Password.
The Console Password protects the console port located (in most cases) at the rear of the router / switch. the syntax to set this password is:
line console 0
login
password
this password is stored in plain text in the running config and can be protected with the service password-encryption command
Telnet Password
The Telnet password protects the router from remote access across a network.
Before setting this password i like to see how many telnet lines i have to play with. To do so, I use the line vty 0 ? command to verify how many lines are available.

Normally, passwords are set on the 1st 4 lines however you can do more if you wish. by not setting the password on the other lines you are not presenting a security vulnerability, you are just not presenting some of the available lines for telnet access
to set the telnet password the syntax is:
line vty 0 4
login
password
This command is stored in plain text in the running config and can be protected with the service password-encryption command:

There are two further security notes with this command. Firstly, its not advisable under any circumstances to use the no login command here. this will allow access into the telnet ports without challenge. Secondly telnet passes information in plain text which is an obvious security concern. For the uninitiated, this mean that the data can be intercepted by tools such as wireshark and easily exploited. instead SSH should be used as a transport protocol here. This will be covered on a further article.
The Auxiliary Password
The Auxiliary port is only present on Routers, not switches. It is used traditionally as a port for remote access via a modem. it is more often used these days as a backup to the console port.
To protect the Aux port:
line aux 0
login
password
As above, this password can be encrypted with the service password-encryption command.:

This concludes the article on setting basic Cisco router and switch security. the information here was presented at a CCNA level. Further articles will go deeper into security hardening a Cisco device.
Thanks for reading!







No comments:
Post a Comment